Fully Managed Technology Services
Organizations with 20–100 employees.
Co-Managed Technology Services
Organizations with 100+ employees with an internal IT team.
Comprehensive Guides

Technical Support
Headquarters
2675 Research Park Drive
Madison, WI 53711
Business Cybersecurity Checklist

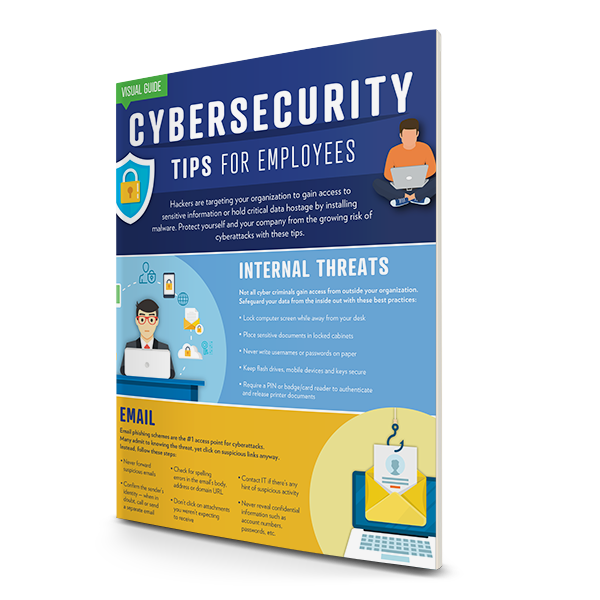
When a cyberattack occurs, most business leaders discover that the method used to gain access to their networks was painfully simple and could have been easily prevented.
Hackers often target businesses that fail to put common best practices in place, many of which are easy fixes and may take only a few minutes.
Use our Business Cybersecurity Checklist to see how you’re doing in five major areas:
- Email phishing scam clues
- Software and hardware loopholes
- Password protocols
- Printer and copier access points
- Disaster recovery and backups
Fill out the form to get your copy and start using the helpful tips right away.
Download Your Free Guide Now
2675 Research Park Drive
Madison, WI 53711
888.733.4060
support@elevityit.com
A Division Of

© 2024 Gordon Flesch Company. All Rights Reserved.
Security Policy | Terms and Conditions
Security Policy | Terms and Conditions

